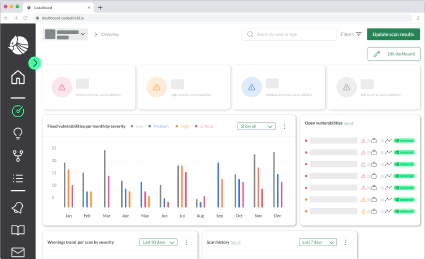
Cloud Security Term: Cloud Infrastructure Entitlements Management (CIEM)
Today, we want to introduce one more cloud security term: Cloud Infrastructure Entitlements Management (CIEM). …

Security experts in an organization usually underestimate the presence of unauthorized cloud infrastructure that is in use, leaving a substantial fraction of the organization’s infrastructure with limited security policy enforcement.
CASB is a software or hardware tool that acts as an intermediary between an organization’s on-premises or remote infrastructure and the third-party service providers it uses. CASB attempts to fill the gaps in security introduced by the fragmentation of security policies while using these third-party services. CASB works as a center for an organization for security policy enforcement.
The “walled garden” approach to security has been the defacto standard for most security-conscious organizations. This policy is an enticing approach since the organization can control the devices, the software on these devices, and the data flowing through them, providing a better model for security, in theory. However, such a model also comes with its downsides. For example, the economics of maintaining and auditing devices and servers, creating specialized software, and the expertise for said tasks, can get out of hand quickly. However, the advantages of outsourcing these requirements to third-party services, in the form of software-as-a-service, platform-as-a-service, infrastructure as a service, etc., brought several undeniable advantages, which led to the proliferation of their usage. Furthermore, these past couple of years have shown us the efficacy of workforce mobility, which led to the growth of the bring-your-own-device policy.
The adoption of these policies changed the “walled-garden” into a patchwork of “fences” where each “fence” can come from a different vendor and can be secure in its own right with various security considerations based on specific attack vectors. However, these “fences” leave gaps when we take a holistic view of security, generating the possibilities of new attack vectors. Since banning such policies will be detrimental for the organization, they need to be managed somehow. That is where CASB comes in. CASB offers various features, including cloud governance and risk assessment, data loss prevention, configuration auditing, malware detections, data encryption, key management, control over native features of cloud services, user and entity behavior analytics, etc.
CASB can be deployed in the cloud or on-premises. Usually software-as-a-service model seems to be quite popular. There are many cloud access scenarios that need to be considered. For example, how does the internal network of a cloud infrastructure stack connects with the on-premises intranet? Another example is where an employee using a privately owned laptop can connect to the on-premises network through a virtual private network. A CASB solution needs to be flexible to change and grow based on an organization’s needs. Many CASB options protect the software-as-a-service components used by an organization. But to have a holistic approach to security, their infrastructure-as-a-service must be protected as well.
A CASB deployment usually offers API control for granular visibility into data, threats, and automated maintenance. A good CASB offering taps into the organization’s existing security strategies, such as data loss prevention, security information, event management, firewalls, etc., to determine the best plans for integration.
A CASB deployment also must offer robust data logging policies for auditing the security in real-time.
CASB is now regarded as an essential part of an organization’s security toolkit. With cloud adoption in organizations being almost universal, the need for observing and maintaining this new patchwork of infrastructure is now paramount.
Today, we want to introduce one more cloud security term: Cloud Infrastructure Entitlements Management (CIEM). …
Running confused deputy attacks exploiting the AWS Serverless Application Repository Early this month at Black …
The cloud security community is filled with different acronyms and it can be hard to keep track of every …