Cloud Security Term: Cloud Workload Protection Platform (CWPP)
Modern software providers across the globe shift their workloads (containers, VMs, serverless …

Today, we want to introduce one more cloud security term: Cloud Infrastructure Entitlements Management (CIEM).
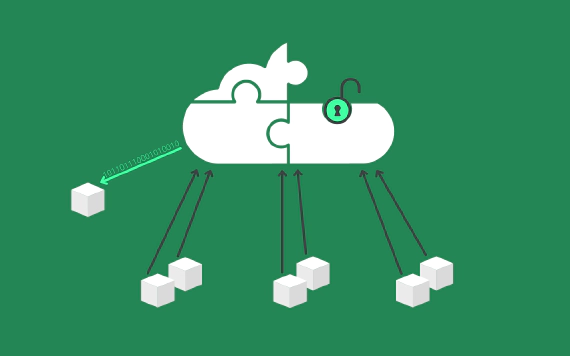
An essential part of every effective cloud security is properly administering identity and access management (so-called IAM) policies to users, workloads, and data (also called entitlements).
As an ever-increasing number of organizations is shifting their applications and workloads to the cloud, the number of cloud users, data, and workloads a security team has to manage increases drastically. This makes it challenging for security teams to assign the policies and permissions to the right actors. To cope with that, organizations rely on Cloud Infrastructure Entitlements Management (CIEM) solutions to properly manage IAM policies in cloud and multi-cloud environments.
CIEM solutions support security teams in applying the Principle of Least Privilege to the cloud resources and services, helping organizations defend themselves against data breaches, malicious attacks, and other risks posed by over-permissioned cloud resources.
IAM policy and entitlement misconfigurations or overly-permissioned resources can happen easily, as anyone within a company may unknowingly or unintentionally give a particular service or user too many permissions. A CIEM tool checks and identifies such errors and overly-permissioned services and users.
Common security risks are overly-permissioned resources, which attackers may abuse to escalate their permissions. An (in-)famous example of the impact of over-permissioning is the Capital One Hack. To avoid the exploitation of excessive privileges, CIEM solutions apply the Principle of Least Privilege.
A typical cloud environment comprises hundreds or even thousands of different identities, e.g., users, applications, cloud services, cloud resources, IoT devices, network components, and so on. All these actors own associated permissions, which grant them access to other actors or data. CIEM solutions help cloud security teams keep track of the different identities, associated IAM policies, and entitlements used in a cloud environment.
To detect any potential threats like permission abuse, CIEM analyzes the existing entitlements against enterprise policies. CIEM flags any suspicious entitlements that violate an organization’s compliance policies and helps cloud security teams by providing mitigation strategies.
To reduce the attack surface and apply zero trust, CIEM solutions can help to apply this Principle by identifying all identities that have access to some resource and recommending reduced IAM policies.
To successfully track identities and entitlements, an properly and up-to-date CIEM inventory is necessary. CIEM tools can automatically inventory and update all IAM policies and entitlements such that cloud security teams and tools, like SIEM can validate them.
To enforce policies and compliance rules CIEM solutions monitor and check cloud environments. To make efficient use of these capabilities, organizations need to define common guidelines for all cloud environments and setups.
CIEM solutions support security teams in applying the Principle of Least Privilege and administering identity and access management in cloud environments. Nevertheless, as a siloed solutions CIEM tools only provide a limited value, a holistic view of the cloud environment in combination with cloud security posture management (CSPM) and risks assessment is a reasonable augmentation that is likely to produce a stronger security posture.
Modern software providers across the globe shift their workloads (containers, VMs, serverless …
The cloud security community is filled with different acronyms and it can be hard to keep track of every …
Running confused deputy attacks exploiting the AWS Serverless Application Repository Early this month at Black …