How to Prevent Code Injection Vulnerabilities in Serverless Applications (Part 1/2)
Recently Serverless application architectures are a trending model for web application development. This is …


Within the last 15 years, cloud computing has become a must-have for almost every company developing or using software. As an increasing number of organizations rely on cloud services or even start shifting to go full cloud-native, cloud security has become a hot topic in the security community. Due to the recent advance of cloud security, the different cloud security terms are not used consistently, leaving their meaning unclear.
Our article series on cloud security will walk you through the most common cloud security terms.
Infrastructure as Code is a technique to automate the definition, provisioning, and management of your cloud infrastructure (e.g., network components, servers, virtual machines (VM), containers, load balancers) through textual code using the principles of traditional software development.
As explained by Kief Morris in the book Infrastructure as Code, 2nd Edition:
Infrastructure as Code is an approach to infrastructure automation based on practices from software development. It emphasizes consistent, repeatable routines for provisioning and changing systems and their configuration.
Before automated IaC tools became popular, admins managed the entire infrastructure manually by installing and configuring each system individually. This manual process led to a set of different problems:
IaC helps organizations to solve these problems by “programming” the steps to provision and maintain the infrastructure in the form of templates and executable scripts. These templates and scripts are treated the same way as source code and put in version control systems like git, leading to the following benefits:
There are several tools in the market that help provision, replicate, and manage complex infrastructures, speeding up DevOps exponentially. Popular IaC tools are
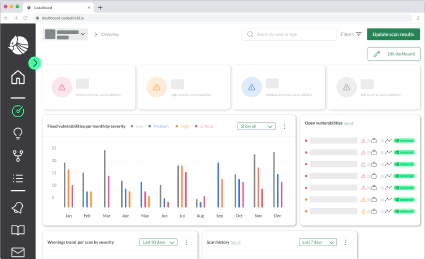
Dangerous network configurations or erroneous permissions in cloud resources may expose critical assets to attackers. Security teams must continuously check IaC templates for security issues without this becoming a hurdle to the pace of DevOps teams. Typical security issues to be checked are:
SSH port 22, public RDP port 3389, or disabled logging that lead to insecure deployments and worst case to data breaches.Infrastructure as Code makes infrastructure configuration and provision flexible and self-explanatory by treating the infrastructure the same way as source code. This enables faster, frequent deployments with secure, error-free processes.

Recently Serverless application architectures are a trending model for web application development. This is …

Checkout Serverless Goat for Java and train your security skills. The code is available under …

This article is Part 2 of a series. Here, I’m going to explain how to secure Serverless applications from …