Log4JShell ByteCode Detector
A remote code execution vulnerability has been recently discovered in the popular Java logging framework Log4j …


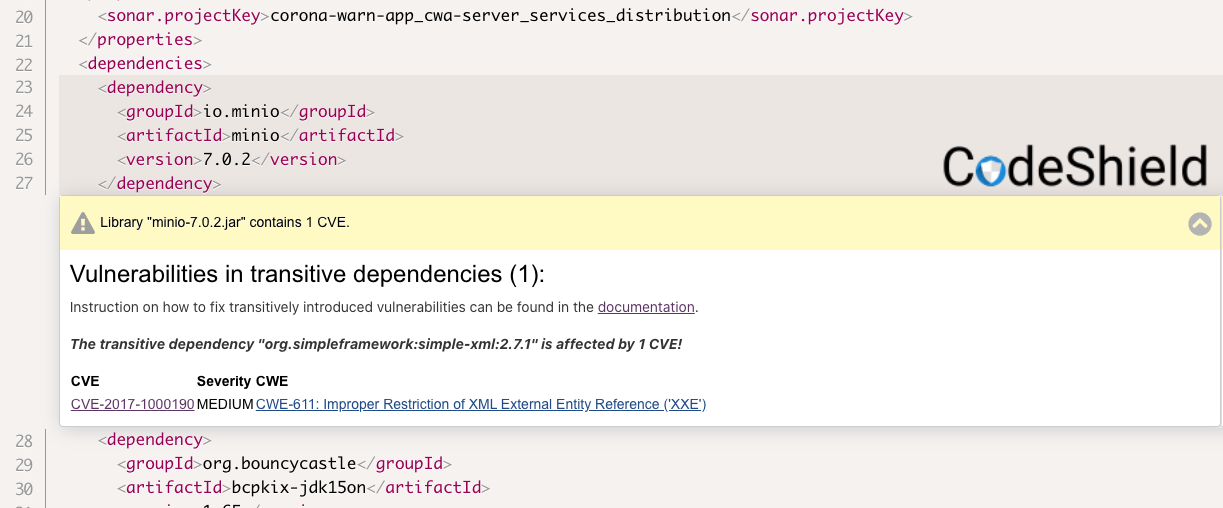
One could call it another proof of concept. But due to the importance of this app, this time there is even more relevance in it: This week we tested the Corona–Warn–App and found some Security vulnerabilities. The Corona–Warn–App, which was jointly developed by SAP and Telekom, was not yet released. Since the source code has been public for some time, we examined it with our CodeShield vulnerability analysis. Result: We were able to find two vulnerabilities, one of which was classified as particularly relevant by our analysis.
We forwarded the info to SAP before the app was published to give them the opportunity to react promptly. The company followed our analysis and was able to patch the vulnerabilities. SAP promptly replaced the affected library. And they mentioned us on the SAP Product Security Response page accordingly. We are glad that we were able to contribute to the security of the app with CodeShield.

It is common nowadays for software to be composed of open-source components. Research shows that even most commercial software products comprise up to 90% of open-source code. However, open-source components are also vulnerable to security vulnerabilities, especially if the latest versions are not used. Keeping track of the vulnerabilities and latest open-source software versions is tedious and difficult manually for developers.
We minimize the effort for developers to find and fix security vulnerabilities in used open-source libraries. With our “fingerprinting” technology, that originated from our research, the entire byte code of open-source components is analyzed for security vulnerabilities. This procedure massively increases the analysis quality compared to common analysis methods, which only searches metadata, and also finds hidden vulnerabilities.
After a long development, we are close to the market launch with CodeShield and are conducting tests with a number of companies. The current case of the Corona-Warn-App and the positive feedback from SAP are another part of the proof of concept for us. Would you also like to see or test CodeShield? Check out our product tour to try it yourself!

A remote code execution vulnerability has been recently discovered in the popular Java logging framework Log4j …

In this blog post, we dive into a comparison of CodeShield versus other existing open-source tools. IAM …

In this post, I want to explain the difference between CodeShield and other cloud security solutions. I …